Two high-tech state police officers have been operating for the last 10 months out of a low-slung building on Industrial Drive, a commercial thoroughfare in Elmhurst where workers labor with keyboards and electrical hookups, rather than their backs. Despite the street name, industry in the neighborhood, which is landscaped with parking lots, appears to be no heavier than a microchip.
Since November, Sgt. Jack Phillips and Special Agent Abigail Abraham have been hacking at video terminals in their portion of a suite occupied by the Illinois State Police Special Operations Unit. Abraham and Phillips also read books and articles about data processing, interview electronics experts and worry about the millions of dollars lost each year through computer fraud.
Sometimes they practically can hear the money as it`s sucked through the cables or hurtled into the air on microwave beams.
Abraham, 29, and Phillips, 37, pace the floor in frustration and imagine all the undetected perpetrators out there–turning bits and bytes into illegal profits, vandalizing entire systems, robbing banks and stores with guile and floppy disks.
The detectives are eager to hear their phone ring. They want to examine tear-stained printouts held in the shaky hands of victimized company comptrollers. They believe they have reached a point where they can help defuse a few logic bombs, collar dumpster divers, nab salami slicers, nail trap doors shut and trip up Trojan horses. Abraham and Phillips know the argot of the electronic underworld now, and they wish the victims would step forward.
”In dealing with computer fraud,” Phillips said on a typical slow morning, ”industry and government have to be able to turn to some law-enforcement agency and say, `We need somebody who can put together a criminal case and prosecute it.”`
So far, he and Abraham are the only agents in the 2,000-officer department to concentrate fully on computer crime. Not many other cops across the country work that beat and nothing else.
James Zagel, director of the state police, came up with the idea a couple of years ago while writing the fraud and larceny segment of a criminal-justice textbook.
”I spent a considerable amount of time researching it,” Zagel recalls.
”I got the distinct impression it is a field which presents significant problems for law-enforcement and significant opportunities for thieves.”
Zagel asked for volunteers and was most impressed with the credentials offered by Phillips, a 12-year veteran with an extensive background in fraud investigation, and by Abraham, a personal computer user and former state trooper with two years` experience rooting out ”mis-, mal- and nonfeasance” among state employees.
Zagel gave his team time and support, sending Abraham off for schooling to the Federal Law Enforcement Training Center in Glymco, Ga., and to computer classes at DePaul. Phillips, meanwhile, was free to pore over the literature and buttonhole data-processing experts.
”The director is hot to trot on this,” Phillips said proudly. ”He`s like a cat in a room full of rocking chairs.”
So far, the team has had only one opportunity to follow through on its knowledge. Last March, officials of Triton College in River Grove called upon the computer-fraud unit after someone used the school`s data processing equipment to alter grades, falsify a transcript and enroll some students into courses for which they hadn`t paid.
The investigation, involving a routine crosscheck of Triton records, led to the June 11 arrest of Donald Moon, 24, a former part-time Triton employee and student. It was not a spectacular debut for Abraham and Phillips, but the Triton College case enabled Zagel to announce with a flourish that his department stands ready to crack down.
”Computer crime is no laughing matter,” the director said on that occasion. ”It is not innocent pranks by teenage hackers. Colorful language like dumpster diving, Trojan horses, trap doors and logic bombs are just different words for forgery, fraud and criminal vandalism. We won`t tolerate it.”
Abigail Abraham, who is given to wearing executive seersucker when she meets the public, can offer more precise definitions of the weaponry.
”A logic bomb,” she explained, ”is a program that`s set to go off after a certain computer operation is performed. It`s designed to render the system inoperative in some way.
”For example,” she said, pulling from her memory one of the classic cases she has read, ”a gentleman in France had taken a divergent path from his employer, and he was the one who had programmed the company`s system from the ground up.”
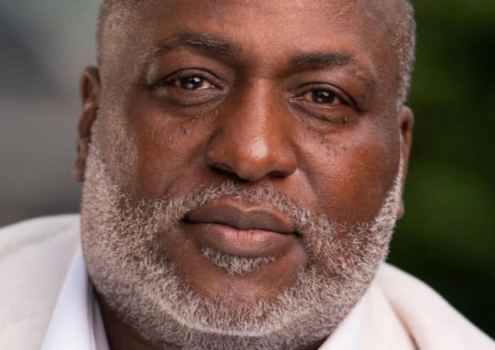
Phillips interrupted, grinning through his beard. ”Stealing from them,” he said. ”That`s the `divergent path,` stealing.”
Abraham smiled gamely. She expects some ribbing from her colleague now and then, because her mode of expression frequently tends toward the academic, probably due to the time she spent at Wellesley College and the University of Chicago. A native of Oak Park, Abraham joined the state police to get a more realistic angle on her criminology studies. After a few months patrolling highways near Peoria, she became addicted to the police life. It may take a while before Abraham completes her degree work and starts writing treatises.
”Anyway,” she continued, ”the programmer and the employer had started the company together. The employer had sort of taken a yuppie track, and the programmer had taken a nerd track, and they became incompatible.
”The programmer ended up getting fired. He was given two weeks` notice, which was a mistake.”
Abraham`s schoolmarmish tones lept suddenly onto a highway-trooper track. ”You don`t give a programmer two weeks` notice,” she snapped. ”You walk up to him and say, `You with the face, LEAVE! Now! I`ll watch you clean out your desk.
”During his remaining two weeks,” she resumed, softly, ”the programmer wrote a program that–exactly a year from the day he was fired–caused the computer to erase absolutely all of the company`s records. Everything. Gone. It killed the company. A logic bomb can cause that kind of destruction.”
Proceeding with their newly learned lexicon, Phillips and Abraham explained that a computer criminal using the salami technique might excise tiny fractions of inventory costs, salaries or withholding taxes and divert them to his or her own paycheck. Oh, how they`d like to slap the cuffs on somebody like that.
Or a crook might insert a trap door into a program, sneaking in a virtually undetectable code that would open up a hole in the security system. A Trojan horse, which is similar to a logic bomb, buries a criminal`s commands within normal instructions and makes the computer do something it`s not supposed to do, such as siphon funds into the perpetrator`s bank account.
”Dumpster diving,” Phillips said, ”is when you go and check the garbage cans and find programs or other useful information in somebody`s trash.” Yes, a little of this criminal activity really does take place in dark alleys, late at night.
Abraham had a dumpster diving episode right on the tip of her lecture notes:
”A guy accessed the mailing list of a cat food company–names and addresses of people who had written in because they were absolutely buggy about the product. (Phillips refrained from pointing out that accessed, in this case, means grabbed.)
”The guy figured that if any people were loony enough to write in about cat food, they must think cats are the neatest thing since sliced bread. So he sent out letters to them, soliciting contributions for a cat cemetery. Perpetual care with a statue of Garfield out front.
”Eventually, the police showed up at his door and asked, `Where`s the cemetery?` The man said, `My backyard.` `How many dead cats do you have?` The man said, `One.`
”Okay, how many dead cats does it take to make a cemetery? Nobody knew. Then the police asked, `Where`s the statue of Garfield the cat?`
” `Well,` said the man, `my son has it. It`s being repaired. And, oh yes, I haven`t had a chance to cut the lawn, so the perpetual care is lapsing a little bit. So what?`
”What are they going to charge that man with?” Abraham wondered. ”He didn`t steal anything from the cat food company. The list was something they threw away. The people were foolish enough to send lots of money for the cemetery. If there had been a provision in the law that would let a judge fine him double the illicit gain, that`s a pretty substantial deterrent.”
Abraham and Phillips have many ideas for laws and penalties not yet spelled out in the Illinois statutes. Most acts of computer sabotage currently are defined as misdemeanors or the mildest levels of felony. Wide areas of nefarious behavior remain unrecognized. Judges haven`t yet ruled on much of it.
On top of all that difficulty, computer specialists with badges cannot find many counterparts in other jurisdictions. Loot and ill-gotten information can cross municipal and state boundaries at the touch of a button these days. Director Zagel said he had trouble identifying role models when he started the unit. The Los Angeles city and county police now employ computer specialists, and so does the U.S. Treasury Department. Other law enforcement agencies, however, rarely organize themselves that way.
Chicago police officials assign computer fraud cases to a 10-detective financial-investigations unit, but no members of the department focus exclusively on transistorized capers.
”There are a lot of computer-assisted crimes,” said Sgt. John Burke, director of the Chicago team. ”It`s considered kind of glamorous now. When an actual computer is the tool, we get calls all the time from the media. If a thief uses a pencil and a ledger sheet, I don`t think there`s quite the fascination.”
His officers do take special courses now and then, but Burke basically looks for detectives who ”understand a systems concept,” he says. ”For a particular investigation, we learn about the system involved and seek the advice of competent witnesses.”
Phillips would have little argument with that approach. A graduate of Lewis College in Lockport, he worked two years as a systems analyst for Allstate Insurance and a year as an Internal Revenue investigator before joining the state police. His pre-electronic investigations usually involved fraud and narcotics.
Abraham, who counts herself as a cop first and a hacker second, has learned to talk Basic on a home computer. She and her partner both realize they will have to deputize a lot of technical experts before they finally pull the plug on all the binary-code racketeers.
”We have to go back to the basics of investigation, no matter what the problem is,” Phillips said. ”My own method, after 12 years in criminal investigation, is to spread all the information out on a desk, build some kind of framework and go from there. When I don`t understand something, I`ve got to find somebody who will be my expert. You run a risk, though, because the person you`re consulting with might very well be involved with the crime.”
Not all outside experts approached by the team have been helpful. ”We thought banks would be prime sources,” said Phillips. ”I forget who said it, but the reason people rob banks is because that`s where the money`s at.”
(Willie Sutton, who had no idea that some day more money might be extracted by computer codes than by guns, usually gets credit for that observation.)
After nosing around a few major banks, Abraham and Phillips came away feeling as if they had asked for a business loan on an Edsel dealership. ”The bankers seemed pretty sure that the safeguards they had in place were doing the job,” Phillips said. ”None of them would admit that they had ever had a problem.”
Various surveys conducted in this decade have estimated that computer crime results in annual losses to business and government of $20 million to $5 billion. The most quoted (and conservative) of these studies, a 1984 American Bar Association query sent to 1,000 private organizations and public agencies, turned up only 72 respondents willing to admit significant losses from computer crime. At a minimum, those losses amounted to an estimated $145 million and might have been as high as $730 million.
The ABA concluded: ”Given the small number of organizations reporting these large known and verifiable annual losses (total and per respondent), the total annual loss figures nationwide would appear to be enormous.”
Phillips and Abraham said they have been told by experts that 90 percent of computer thefts are inside jobs and, therefore, embarrassing. ”Rarely,”
said Phillips, ”are you going to find somebody sitting in his basement and tapping into a bank`s computer system so that bundles of money are delivered to 83d and Cottage Grove at midnight on a Friday.”
Prosecutors may wish that were the case. The computer fraud team has been dreaming up scenarios for several months, and they frequently involve nightmarish entanglements with statutes and the rules of evidence.
Phillips put it this way: ”As soon as you walk into a state`s attorney`s office and say, `I want a prosecution on a computer-fraud statute,` all of a sudden everybody gets the hives. The state and federal computer-fraud statutes on the books are certainly not a trip to Hollywood.”
He reached into his desk and pulled out the Triton College file, a folder of documents somewhat thicker than a Chicago phone book. ”We got some felony charges,” Phillips said. ”The Cook County states attorneys were very receptive. But this is what the paperwork looks like, and this is a no-big-deal case compared to sophisticated computer fraud.”
At least it was a start. Abraham and Phillips currently have the time to sit back and envision big investigations yet to come. They think about sting operations using electronic bulletin boards. They imagine characters who, even now, are doctoring electronic invoices and diverting shipments of goods to scattered henchmen. They ponder the workings of credit-card rings, vandals with keyboards, bookie networks, stock market scams. . . .
”In the future, we may not have much time,” Phillips said, ”but right now, just mention the word `computer` to us and we`ll come right out and talk to you.”