Since the Persian Gulf war, computer experts and military strategists have been toying with a chilling new concept in warfare: Knocking out an enemy`s weapons by ruining his computer systems with viruses designed to throw off or reverse the commands originally programmed.
In 1990 the U.S. Army, acting through the Defense Department and Small Business Administration, solicited bids on a contract for feasibility studies on the idea.
Most information about the program is classified, but Army spokesman Henry Kearney said such a plan is being investigated at the Center for Signal Warfare in Ft. Monmouth, N.J.
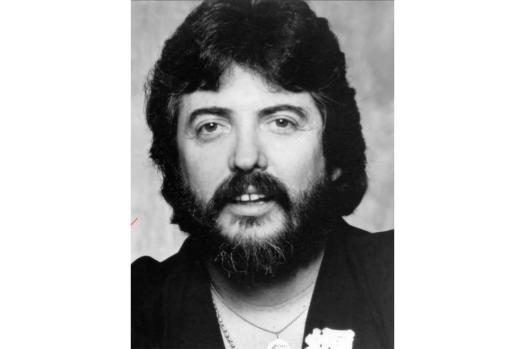
Some companies doubt the concept is workable, including John McAfee Associates of Santa Clara, Calif., which was invited to submit a proposal.
McAfee Associates, which develops antiviral software for IBM computers, turned down the job.
”It basically asked, `What can I do with viruses to disrupt enemy computer systems?` But we felt it was impossible,” McAfee said. ”Nothing is impossible in electronics, but we felt this was beyond the realm of our capability and most capability using today`s technology. In 5 or 10 years, I can`t say.”
If not impossible, the concept may be too chancy, according to Russell Brand, a computer virus expert at Reasoning Systems Inc. of Palo Alto.
”Creating the virus is easy,” he said. ”The question becomes, how do you get it on the computer you want to attack and how do you get it to go off at the right time?
”Viruses are programs that insert themselves into other programs. You don`t know where they`re going to end up and interact with other things. It`s hard to figure out how to trigger them at the right time. You can`t predict what day war (will) start.”
He speculated that an enemy plane could be shot down by its allies because a virus had turned off its computer system. Other sabotage could turn around missiles and direct them to blow up home base.
If an enemy learned that Americans had such capability, the technology could also reach enemy hands, and both sides would be in the same boat, some experts said.
Steve White of IBM`s High Integrity Computing Laboratory in Hawthorne, N.Y., said trying to infect an enemy computer with a virus is like ”trying to give the enemy the common cold and hoping only the enemy gets it.”
White said it may be possible to inject a virus into an enemy computer via a radio link. His IBM group does research on anti-virus software, seeking to develop stronger safeguards against program invasion.
”Any security system can be compromised,” said Peter Neumann, principal scientist at the SRI International computer science laboratory. ”The virus is the tip of the iceberg. Computer systems are vulnerable from attack not only by outsiders, but also by trusted insiders.”