In Chicago, only the FBI and Secret Service have one. But on August 30, Wright College became the third Chicago institution to operate a computer forensics and security lab.
The government institutions use their labs to track down high-tech criminals who access, steal or share proprietary data.
The lab at Wright College (http://wright.ccc.edu/department/forens ics/index.asp) is designed to turn students into practicing professionals of the computer forensics industry.
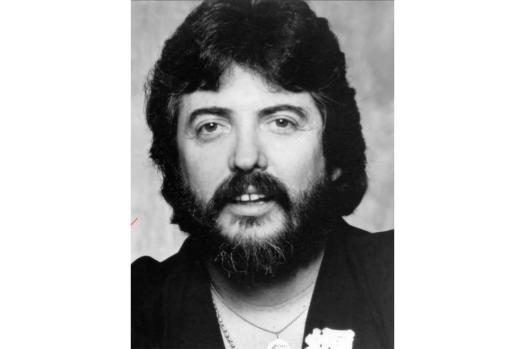
“In a nutshell, these [students] will protect information and systems from viruses, hackers and illegal intrusions,” said Cyrus Walker, the 33-year-old head of Wright’s computer forensics lab.
With input from the FBI, about $500,000 in hardware and software donations from technology security firms like GuardedNet (www.guarded.net) and Lancope (www.lancope.com) and $250,000 of Wright’s own money, the lab opened with 15 “benchtop” computers and 10 networking racks.
There are about 40 students enrolled in the two-year certification program (no degree is available), at a cost of about $1,500 for Chicago-based students and upward of $5,500 for out-of-district attendees.
“A student doesn’t have to be attending Wright College to participate in the program,” Walker said. “In fact [students can] incorporate our certificate into their studies elsewhere.”
Once their education is complete, the new practitioners can enter the real world, where corporate IT departments find themselves in a daily race to stay one step ahead of–or, for some, catch up to–hackers.
“There are two perspectives to protecting information,” said Walker. “Companies must protect their system from the outside world and the inside world.”
Outsiders are those trying to access corporate computers from the Internet. Walker said several layers of protection are required to secure systems from this risk.
“You have to understand what needs to be accessed by the world, and what is protected,” he said.
Walker explained that firewalls and antivirus tools are required for such protection, but are no longer enough:
– Intrusion-detection systems–“which monitor transactions coming into and going out of the network”–range in price from free to more than $50,000, depending on size and complexity of the computer network.
– Security information management, which is a process of analyzing logs of network traffic to identify inconsistency and unauthorized activity, can run upward of $50,000.
– An encryption element is also a necessity to a company’s information defense plan, so that data leaving the corporate servers is scrambled and unreadable to outsiders.
– A big-picture understanding of vulnerability is also helpful, and vulnerability assessment programs can be used to identify, analyze, and report potential holes in a company’s operating system, routing protocols and firmware.
But while keeping out intruders is a major part of an IT department’s security function, it must also defend the firm’s data against disgruntled employees–or insiders.
“The key is to establish policies for how people can use the Web,” Walker said. “And a regular review of the information system usage policy is key. It does no good to just hand the employee a manual and never go over it again. I would do a six-month policy review with staff.”
– – –
Some keys to security
– Two network security applications are made by eEye Digital Security (www.eeye.com): Retina (a vulnerability assessment program retailing for about $8,000) and Iris (a network traffic analyzer for about $1,800).
– A free network intrusion-detection system called Snort, manufactured by Sourcefire, is made available at www.snort .org.
– RSA Security (at www.rsasecurity.com) is the leader in encryption software, according to Walker, and offers encryption tools ranging from about $300 to over $200,000.
— Alex Goldfayn
———-
Contact alex@technologytailor.com